dVPN (DPN) vs VPN: what are the differences and which one to choose?
VPNs are widely trusted as the standard tool for online privacy, but not all VPNs work the same way. Behind the familiar interface, centralized and decentralized VPNs operate on fundamentally different models of trust, control, and data exposure. These differences affect who can see your traffic, how censorship is bypassed, and what happens when authorities come knocking. This guide breaks down how VPNs and dVPNs really compare, and which one fits your priorities.

Key takeaways
- Centralized VPNs require trust in a single company that controls servers, encryption keys, and potential access to user data.
- Decentralized VPNs reduce tracking risk by design, since no single entity can see a complete browsing session.
- Residential IPs used by dVPNs are harder to block, making them more effective against censorship and VPN blacklists.
- Ease of use, pricing models, and legal exposure differ significantly and often matter more than raw encryption strength.
Most of us probably cannot imagine a life without the internet anymore. We use it for leisure, conducting business, communicating, and, in general, sending and receiving huge amounts of information. If not protected, that information can fall victim to bad actors and oppressive governments who are always seeking to take advantage of internet newbies.
For regular users, an easy-to-use web security tool such as a VPN is more than enough. However, they have two main types that can be confusing: VPN and dVPN.
A VPN (Virtual Private Network) is a cybersecurity tool that provides a secure, private connection over the internet, like a hidden tunnel, allowing you to safely send and receive data without others seeing what you’re doing. One of the main uses of a VPN is to connect to servers abroad to hide your IP address and appear as if you are browsing from another part of the world. This is a broad term used both for defining the tool category and indicating a traditional, or centralized VPN, an older, more common type of VPN. A VPN is considered centralized when the tool provider owns both the servers you connect to and the software used for the connection (the client).
A dVPN (or DPN) is a decentralized Virtual Private Network, built on a community of independent server providers across the world, instead of a single company that owns everything. The terms dVPN and DPN are used interchangeably, but dVPN is the more accurate option since it explicitly references the VPN concept - it is, after all, a virtual, not physical tool.
When we compare a VPN vs a dVPN, the main similarities are:
- Basic concept. Both protect your data when browsing the web by encrypting and sending through a secure tunnel.
- IP Address Masking. Either can be used to connect to a server abroad, hiding your real IP address.
- Compatibility. Both VPNs and dVPNs are typically available across multiple platforms: smartphones, tablets, computers, smart TVs, or routers.
The most notable differences between a VPN vs a dVPN are:
- Server ownership. The connection points of a decentralized VPN are owned by regular people or companies not affiliated with the dVPN service provider. They offer the possibility to connect to their computers in exchange for various incentives. A centralized VPN, on the other hand, owns or rents all of its servers and maintains them directly.
- Need for trust. When connected to a VPN, all of the users’ traffic is passed through a single company, which needs to be trusted to not share/use that data for bad purposes. A dVPN sends user traffic through a randomly selected shared server (also called a node), greatly reducing the risk of anyone seeing the full picture.
- Pricing. Whereas traditional VPNs have fixed, subscription-based pricing for users, dVPNs often employ usage-based pricing (commonly in cryptocurrency), so they only pay for the services they use.
dVPN vs VPN: What’s the Difference?
Below we have grouped the main differences between the two types of tools for your convenience.
Technology and infrastructure
A centralized VPN has a simpler infrastructure than a decentralized VPN. As the name implies, all of its tech lies under the same, figurative, roof. The software you use to connect (called a client) and the servers you connect to belong to the same company.
A centralized VPN’s servers are massive and host thousands of connections simultaneously, with many different users being given the same IP address. The service provider earns funds by charging a subscription fee to its users (unless it’s a free VPN).
Decentralized VPNs are more complex. The service provider only owns the client, whereas the servers you connect to are owned by independent community members. These connection points are called nodes. The bulk of connectable nodes belong to individual users who share their personal IP addresses.
Some dVPNs incentivize node providers by rewarding cryptocurrencies for sharing their unused internet bandwidth. It could be direct usage-based peer-to-peer micropayments between the dVPN user client software and node provider software. Alternatively, a dVPN company can charge a subscription fee to their users and pay the node providers directly.
Privacy and anonymity
Privacy is the main reason why most users connect to a VPN. As a user, you want your browsing data to be unidentifiable: both by other people on the internet and by the VPN you are using.
Regardless if you are using a VPN or a dVPN, your connection is encrypted and secured in the same way while browsing the web. The biggest difference in terms of your privacy is how your data is exposed to the service provider itself.
As mentioned before, centralized VPNs own and see each step of your connection to the web. As a result, the service provider has the theoretical possibility to see all of your browsing data. Whether they keep that data secret is a matter of trust. For example, TechRadar mentions that 71% of free Android VPNs share user data with third parties.
dVPNs, on the other hand, are designed with user privacy in mind. Due to its structure, no single entity has access to all of your data, which makes it considerably less likely for the service provider to employ any meaningful tracking.
Security
Security is another of the main reasons for investing in a VPN. As a user, you want your connection to be encrypted and safe from hacker attacks.
It can be argued that the servers of a centralized VPN are better protected against hackers since the VPN companies have to protect their infrastructure. Yet some VPN servers are connected to by thousands of users at a time therefore they become lucrative targets for bad actors trying to steal data.
The security of dVPN nodes varies: individual node provider computers might only have the protections provided by the operating system and the dVPN provider software, while nodes deployed in data centers might employ protection more akin to centralized VPNs. This should not cause concern, however, as the smaller traffic of a singular dVPN node and the concept that the node provider doesn’t have the knowledge of dVPN users makes it a significantly less important target for hackers.
Finally, both centralized and decentralized VPNs most often use the same industry-standard methods for securing their connection, such as AES-256 encryption and tested, open-source VPN protocols like OpenVPN or WireGuard. Be cautious about VPNs that don’t have these technologies in their arsenal.
The biggest difference here is the entity that holds encryption keys, which allow the service to encrypt and decrypt your browsing data. Centralized VPNs keep all of their encryption keys, which can be a problem if they fall victim to hackers, as all users might become vulnerable. With a dVPN, every node encrypts data individually, so even if it did get hacked, only users connected to that specific node would be at risk.
No-Logs policy
A No-Logs policy is a promise made by a VPN company to not collect any data related to its users’ browsing activities. Even though sometimes these policies are reinforced by independent audits, they are still, at their core, just a promise. These audits are a snapshot of the VPN’s activities at a single point in time, which means that user tracking can be set up right after, in theory at least.
A centralized VPN has all the technological means to track its users since it owns all of the steps of a customer’s connection. A decentralized Virtual Private Network, on the other hand, is designed with a true No-Logs policy in mind. The node provider can only see that someone is using their connection - the user identity is hidden.
Speed and performance
In terms of speed, there isn’t a significant difference between the two alternatives.
Centralized VPNs boast high-bandwidth servers that can handle high amounts of traffic and make significant investments into infrastructure to realize these claims. Keep in mind, however, that some locations are more popular than others - for example, servers in the USA might not deliver the performance you require during peak hours.
On the other hand, decentralized VPNs offer so-called residential IPs - connections hosted with personal home computers and data center IPs, which, as the name implies, are provided by server clusters. Residential IPs have the theoretical internet speed of a regular user’s internet connection. This might cause some concerns, but since the selection of nodes is generally much greater than the amount of centralized VPN servers, the supply and demand for connections balance out the connection speed comparable to centralized VPNs. If you do have a need for the fastest option of safe internet browsing, simply choose a datacenter IP.
Accountability and transparency
Accountability and transparency are what you want from a company you pay for protecting your data. Things that contribute to them are a VPN’s user data policy, honesty about mistakes, responsibility for damages, and more.
No VPNs are required to be fully transparent about their operations or accountable for failures, your relationship with them is solely based on trust. Of course, if information about a data leak is made public, the VPN company can be made accountable by law, especially if it happened due to the company’s negligence. However, as of August 2024, no past VPN data breaches reported by VPNLeaks have received legal action by a government.
This is why it’s crucial to choose a VPN that is the least likely to mess with your browsing data, which is where the presence of a No-Log policy helps.
dVPNs do not have the technical means of tracking all of your activities online and are therefore more likely to keep the No-Logs policy promise. In contrast, centralized Virtual Private Networks can theoretically see all of your browsing data although in most cases the data is encrypted by the HTTPS protocol or other end-to-end encryption methods.
When choosing a VPN, make sure that it:
- Hasn’t fallen victim to a data leak before
- Has a No-Logs policy
- Tracks as little of your activity as possible
Usage and compatibility
To be protected everywhere and at any time, you want your VPN to be compatible with all of the devices and operating systems you use.
There isn’t a significant difference between device compatibility between centralized and decentralized Virtual Private Networks. The biggest difference lies in the resources those companies have to invest in developing apps for different operating systems and devices, add-ons for browsers, and alternative ways to connect. Centralized VPNs often have bigger development teams and budgets for making their service available to all possible use cases.
Nevertheless, most dVPNs are available on Android and Apple smartphones, together with Windows, Linux and iOS computers, which make up the bulk of ways you will use the app. According to Forbes, 72% of users have VPNs on their PCs and 69% on their smartphones.
Circumvention of censorship
Beating censorship by progressive governments is one of the most common reasons for investing in a VPN. As political activists move their discussions online, oppressive governments increasingly shut down the internet to silence protestors. The authoritarian regime of Turkey, for example, has shut down its own internet 13 times since 2015, according to a report by Surfshark and Netblocks.
VPNs are not completely resistant to government bans either. They are one of the most common ways to circumvent censorship, so it makes sense for a regime to restrict their use as much as possible. Established centralized VPNs possess connection obfuscation techniques to combat some VPN restriction measures such as DPIs (Deep Packet Inspection).
However, one of the most common ways to limit VPNs is to simply ban the IP addresses they use. Centralized VPNs use a limited amount of IPs per location, which are found in IP address lists governments can acquire. On the contrary, decentralized VPNs allow you to connect to IPs of individual people (residential IPs), which are significantly more difficult to find and ban.
User experience
Centralized VPNs are most often designed for users with low technical skills and, as such, as very easy to set up. Some decentralized VPNs might be more challenging to use, as they’re based on more complex technology overall.
As always, there are some exceptions to the rule. Some dVPNs (like PortalsVPN) maintain a healthy balance of being able to connect to personal nodes via a convenient and understandable user interface. Just pick a country you’d like to connect to and voila - you’re ready for safe browsing.

Cost
When it comes to payments, centralized VPNs generally offer fixed periodical pricing, while variable pricing is more common with dVPNs.
Centralized VPNs focus more on subscription-based payments, with a fixed amount paid periodically for the right to use the software. Usually, you may get a discount when purchasing a subscription for a longer period (e.g. 1 year). Be aware though that in most cases, the subscription is automatically renewed at a higher undiscounted price after the first subscription period ends. Keep in mind that the subscription price doesn’t change whether you use the service or not.
With decentralized VPNs, the most common method is to charge customers depending on their usage of the service. The more bandwidth you use, the more you pay.
Some dVPNs make it easier for users and offer subscription-based pricing. PortalsVPN has easy-to-understand subscription plans and any discount you get will be applied to renewals automatically.
Payment methods
Centralized VPNs and some dVPNs accept payments in the major world currencies such as the US Dollar or Euro. If you are really passionate about concealing your identity, some VPNs accept payments in cryptocurrencies like Bitcoin (BTC), Ethereum (ETH), and even Dogecoin (Doge).
Some VPNs like ProtonVPN or Mullvad even accept payments in cash (sent in an envelope to their headquarters) for those who prefer to keep things old-school.
Legal considerations
Since VPNs are often used to circumvent censorship, access blocked content, and sometimes even engage in illegal activities, their relationship with some national governments is complicated.
Both VPNs and dVPNs are legal to use in most countries around the world. All VPNs are illegal in:
- Turkmenistan
- Iraq
- Egypt
- Belarus
- North Korea
Some countries haven’t outlawed VPNs per se, but possess restrictions on their use, such as only making state-approved VPNs available (these allow oppressive governments to access user data at will). These countries are:
- China
- Russia
- Turkey
- The United Arab Emirates
- Egypt
- Oman
As both VPNs and dVPNs are operated by legal entities (read: companies), they have to operate within the laws of the country they are based in. If a government agency wants to access the data of a specific user that might have broken the law, these companies have to hand that data over, as long as they are under the inquiring country’s jurisdiction.
Whereas centralized VPNs can keep their user data in some shape or form, dVPNs simply have fewer means to do so - anonymous browsing data is only accessible by the node used for connection, and in most cases, data is encrypted end-to-end using protocols like TLS.
In addition, a government might seize the physical servers of a centralized VPN provider. For example, the Ukrainian authorities confiscated Windscribe’s unencrypted local servers in 2021, as reported by Ars Technica. Such an action would be very difficult against a dVPN company, as nodes are anonymous, difficult to identify, and are spread out around the globe. In addition, the breach of a single node would not compromise the rest of the network, as each node is encrypted separately.
Server locations
The variety of server locations is paramount to any VPN user. With a single VPN that has a wide array of servers, you can do many cool things:
- Watch streaming services from countries with the biggest libraries, such as the US, the UK, or Slovakia (yes, Slovakia has the biggest Netflix library in the world, according to industry data by Statista).
- Take advantage of price discrimination by buying the same products for a fraction of the price when connected to countries with a lower median income like Ukraine, Turkey, or Peru.
- Always connect to a server close to you for maximum speed, no matter where you travel.
If we were to compare centralized and decentralized virtual private networks, the latter would come out ahead in terms of the variety of server locations. Since centralized VPNs rely on huge servers that the VPN company has invested in, naturally there will be fewer of them. In contrast, setting up a dVPN node does not require any special hardware. Anyone with a PC or even just a mobile phone, internet connection, and a little bit of technical knowledge can set up a dVPN node. Naturally, the worldwide coverage of a dVPN can be better.
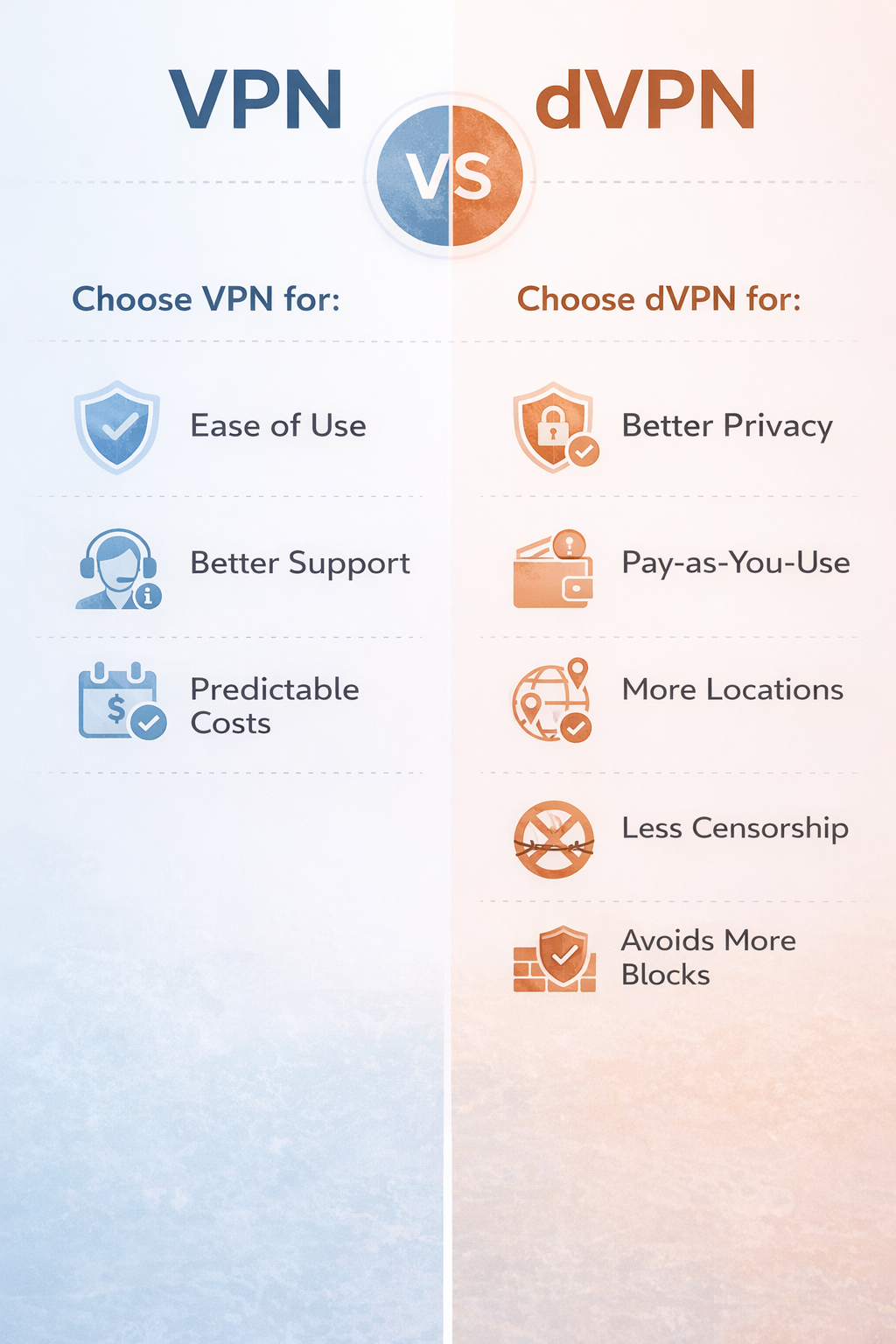
VPN vs dVPN: Pros and Cons Summarised
| Category | Centralized VPN | Decentralized VPN (dVPN) |
|---|---|---|
| Technology and Infrastructure | Simpler infrastructure; the VPN provider owns both the client and servers. Servers are massive and host thousands of connections simultaneously. | More complex; the dVPN provider owns the client, while nodes are owned by individuals. |
| Privacy and Anonymity | The VPN provider might be able to access unencrypted browsing data; privacy depends on trust in the provider. | Designed for privacy; no single entity has access to all data, reducing the possibility of tracking. |
| Security | Centralized servers are well-protected but are more lucrative targets for hackers. | Security varies by node; smaller nodes are less attractive targets, but protection levels can vary. |
| No-Logs Policy | The provider can technically track all unencrypted user activity; No-Logs policy relies on trust. | Built with a true No-Logs policy; the dVPN provider has limited and only theoretical access to user activity. |
| Speed and Performance | High-bandwidth servers that handle large amounts of traffic, though some locations may be congested. | Varies depending on node; residential nodes offer average speeds, while data center nodes can match centralized VPN performance. |
| Circumvention of Censorship | Some centralized VPNs provide the possibility to use obfuscation techniques to bypass censorship, but limited IPs make them easier to block. | Residential IPs make dVPNs harder to block, offering better censorship circumvention. |
Are decentralized VPNs safer than traditional VPNs?
Yes, decentralized VPNs are safer than traditional VPNs. Their decentralized infrastructure makes it much more likely that no single entity has access to all of your data, making tracking extremely unlikely. In addition, if hackers were to breach a single dVPN node, the rest of the network would still be inaccessible to them.
Advantages and disadvantages of a decentralized VPN
The advantages of a decentralized VPN relate to better privacy and more freedom when using and paying for the service. The disadvantages are centered around the complexity of the user experience.
Advantages of a decentralized VPN
- No tracking. The infrastructure behind decentralized VPNs reduces the possibility of the dVPN provider from tracking your browsing.
- Pay-as-you-go. With most dVPNs, you only pay for the bandwidth you use, with no flat fees.
- More server locations. Since setting up a dVPN node is much easier than a centralized server, there are more to choose from.
- Less government intervention. As dVPN providers don’t have access to browsing data, and nodes in the network can’t identify their users, it’s nearly impossible for the government to collect the browsing data of a particular individual.
- Better at beating censorship. Residential IPs allow users to avoid VPN IP blacklists and other measures implemented to block VPN use by oppressive governments. The same applies to web services, such as streaming websites.
Disadvantages of a decentralized VPN
- Requires technical knowledge. Most dVPNs are designed for tech-savvy users and are more difficult to set up than their centralized counterparts. Others though, like PortalsVPN, feature a simple user interface.
- Unfamiliar node hosts. With decentralized VPNs, you don’t really know who has set up the node you are using. However, your connection is encrypted, making it very difficult for the host to identify who you are.
- Complex payments. Most dVPNs use complex pay-as-you-go payment systems which require a cryptocurrency wallet. If this is an issue, consider choosing a dVPN that offers subscription options, such as PortalsVPN.
Advantages and disadvantages of a traditional VPN
The advantages of a traditional VPN stem from its accessibility and ease of use, while the disadvantages arise from its accountability to governments and the risk of customer data misuse.
Advantages of a traditional VPN
- Easy and quick to use. Traditional VPNs can be set up in minutes and don’t require specific technical knowledge to use.
- Customer support and guides. Reputable centralized VPNs have customer support specialists reachable in different ways to help you with any problem. For users that prefer solving issues themselves, FAQs, tutorials and troubleshooting guides are available.
- Predictable cost. With a flat subscription fee, you will always be paying the same amount, even if you use the service extensively.
Disadvantages of a traditional VPN
- Privacy based on trust. The whole infrastructure of a centralized VPN belongs to the same company that could track your activities. Your relationship with them is based entirely on trust.
- Less effective against censorship. Centralized VPNs can’t offer as many IPs as dVPNs and many of those offered are being blocked by streaming services and oppressive governments.
- Susceptible to subpoenas. Traditional VPNs comply with the laws of the country they’re based in. If a government agency wants access to their user data, it will have to be handed over.
Can you use both dVPN and VPN simultaneously?
No, you cannot use both a dVPN and VPN simultaneously to improve your privacy. This is because such a connection can face various problems, like network configuration issues, IP address conflicts, and routing errors. VPN services are typically configured to run on their own and likely won’t work with another VPN connection layered on top, so you will not be able to avoid both dVPN and VPN disadvantages at the same time.
If you are looking to add another layer of security to your connection, consider Tor over VPN as some VPN services provide such a possibility. This is a technique that relies on using the Tor network over your VPN connection. Keep in mind that it’s not applicable to all use cases: while it greatly improves your security, it also significantly reduces your connection speed and has other known downsides like raising a red flag to the authorities, constantly attracting Captcha tests, etc.
So which is better - VPN or dVPN?
For most use cases, a decentralized VPN is a better choice than a VPN.
A dVPN provides more locations for taking advantage of price discrimination - connecting to servers in third-world countries allows you to buy products and services online for less, as vendors often adjust prices to the living standards of each country.
Adding to that, dVPNs provide their users with residential IPs to avoid censorship or access their favorite content online. Also, their inherent architecture greatly reduces the chances of getting tracked by the dVPN service provider, as it doesn’t have access to browsing data, contrary to a centralized VPN. This is also good for anonymity because, as a result, dVPNs are unlikely to be able to hand over your browsing data to authorities if requested to do so.
These are the reasons why we think a decentralized VPN is generally a better choice.
Centralized VPNs also have some merit. They usually have very active technical support and a variety of guides for self-troubleshooting. Finally, most of them are easy to set up and feature a predictable cost structure.
In conclusion, no matter which VPN type you end up with, remember to choose a service that stands on all of these three pillars of trust:
- Hasn’t fallen victim to a data leak before
- Has a No Logs policy
- Tracks as little of your activity as possible.
Happy browsing!